Users Overview
Heimdall currently provides a built-in user database that allows individual users to have defined authentication (password) and login locations defined.
Further, if desired, a user can be configured as a read-only user, and Google Authenticator compatible two-factor authentication.
Internally, passwords are stored in the same way that OpenLDAP stores them by default, i.e. Salted SHA. Example, {SSHA}cca9bbffe6879f8367ab681952da2f995bf1668f
Configurable fields can be found in: Users
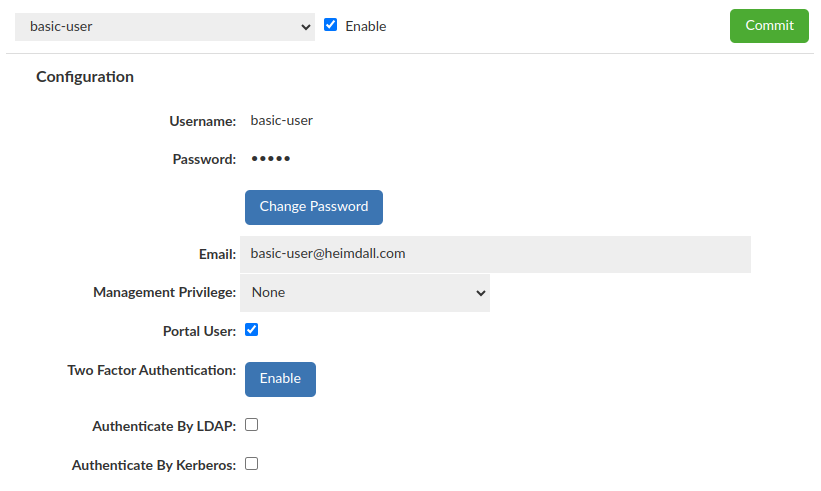
Basic User (with Portal Mode enabled)
Require "Username", "Password" and Portal User enabled
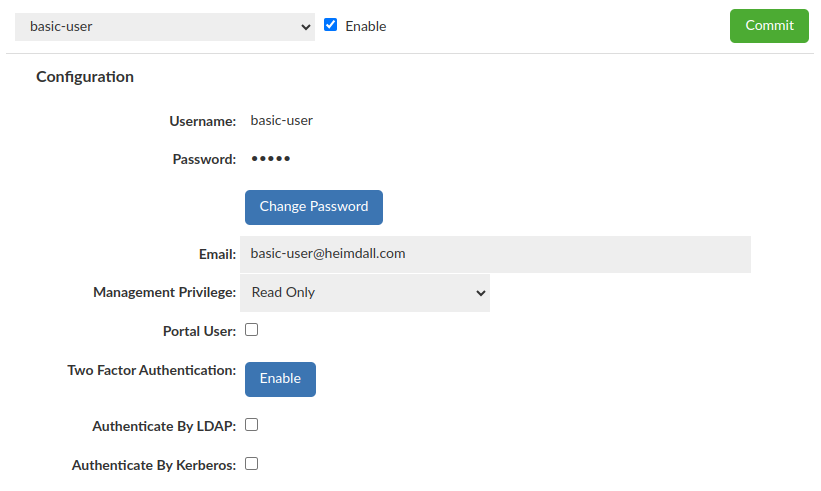
Basic User (without Portal Mode enabled)
Require "Username", "Password" and selected Management Privilege
Kerberos user
Require "Username" and "Authentication mode: Kerberos"
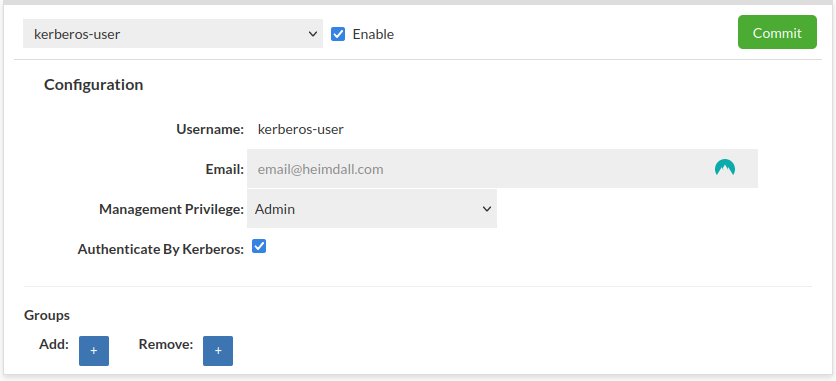
More details about Kerberos Configuration here.
LDAP user
Require "Username" and "Authentication mode: LDAP"
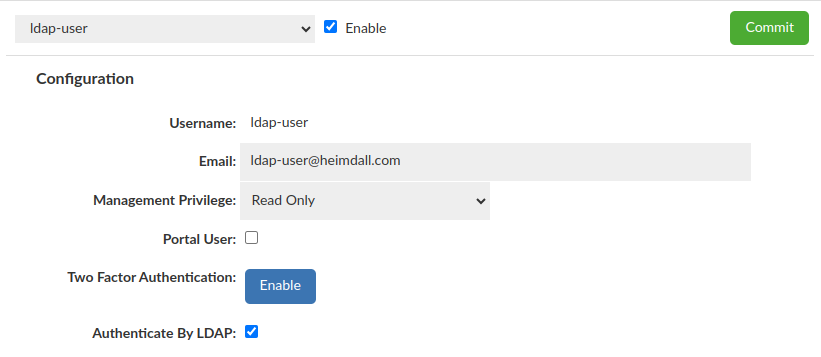
More details about LDAP Configuration here.
If there is only one LDAP Configuration available, it will be used by default. Otherwise additional dropdown "LDAP Configuration" will appear to specify which config should be used with a particular user.
SAML2 user
Require "Username" and "Authenticate by: SAML2"
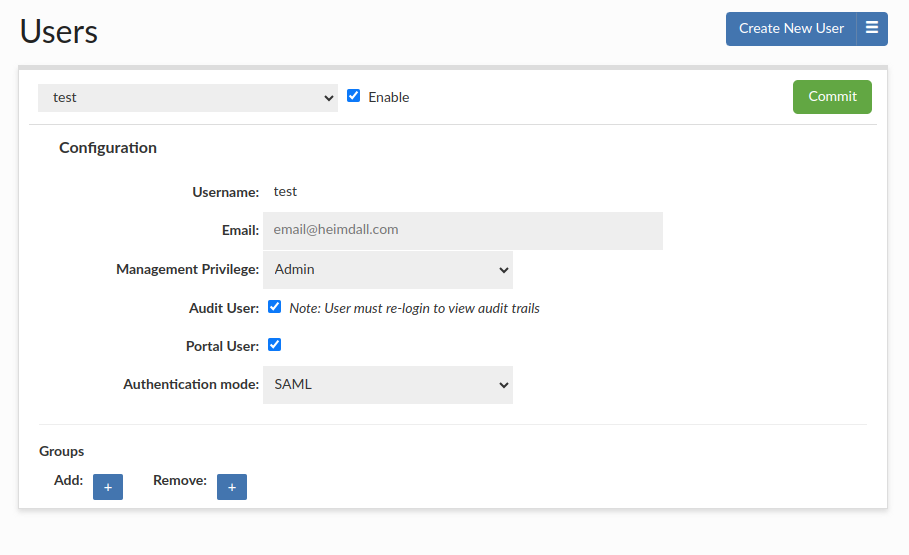
You can set up SAMl2 Configuration in the SAML 2.0 Configuration Guide. SSO can be configured using saml2 auth with AWS IAM Identity Center, Okta, or other saml2 identity providers.
IAM user
Require "Username" and "Authenticate by: IAM"
When using IAM access, appropriate access to the IAM role should be configured for the management instance.
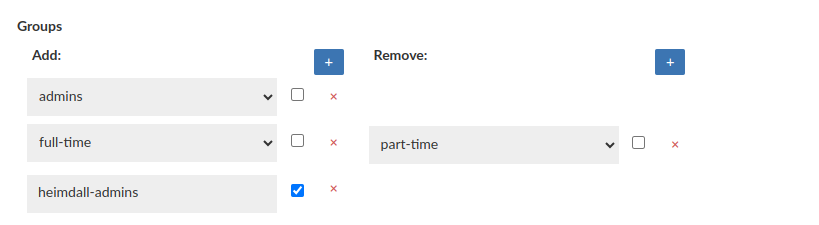
Groups
This feature is available for all Heimdall (GUI) users, doesn't mather whether user authenticates by LDAP or not.
This one allows to grant or revoke a group membership for testing purposes, e.g for LDAP based notifications (Notifications tab in admin tab).
For enhanced security measures, it is imperative that at least one real LDAP Group be extracted when utilizing this feature while using for LDAP authentication testing purposes.
What is important configuration applied there DOES NOT IMPACT the real groups membership on LDAP Server.